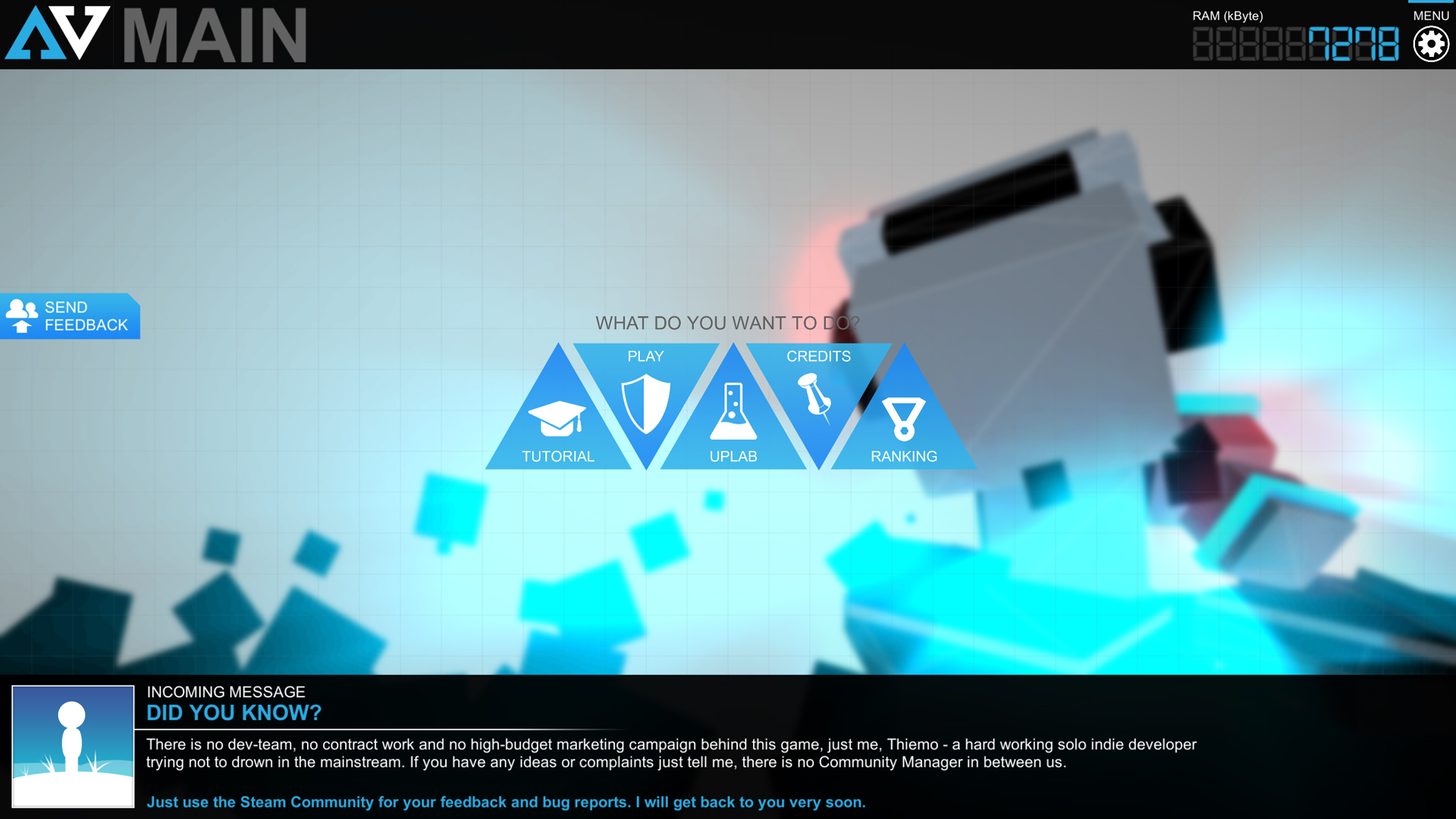
Разработчик: Thiemo Bolder, ONEMANGAMES
Описание
In a nutshell:
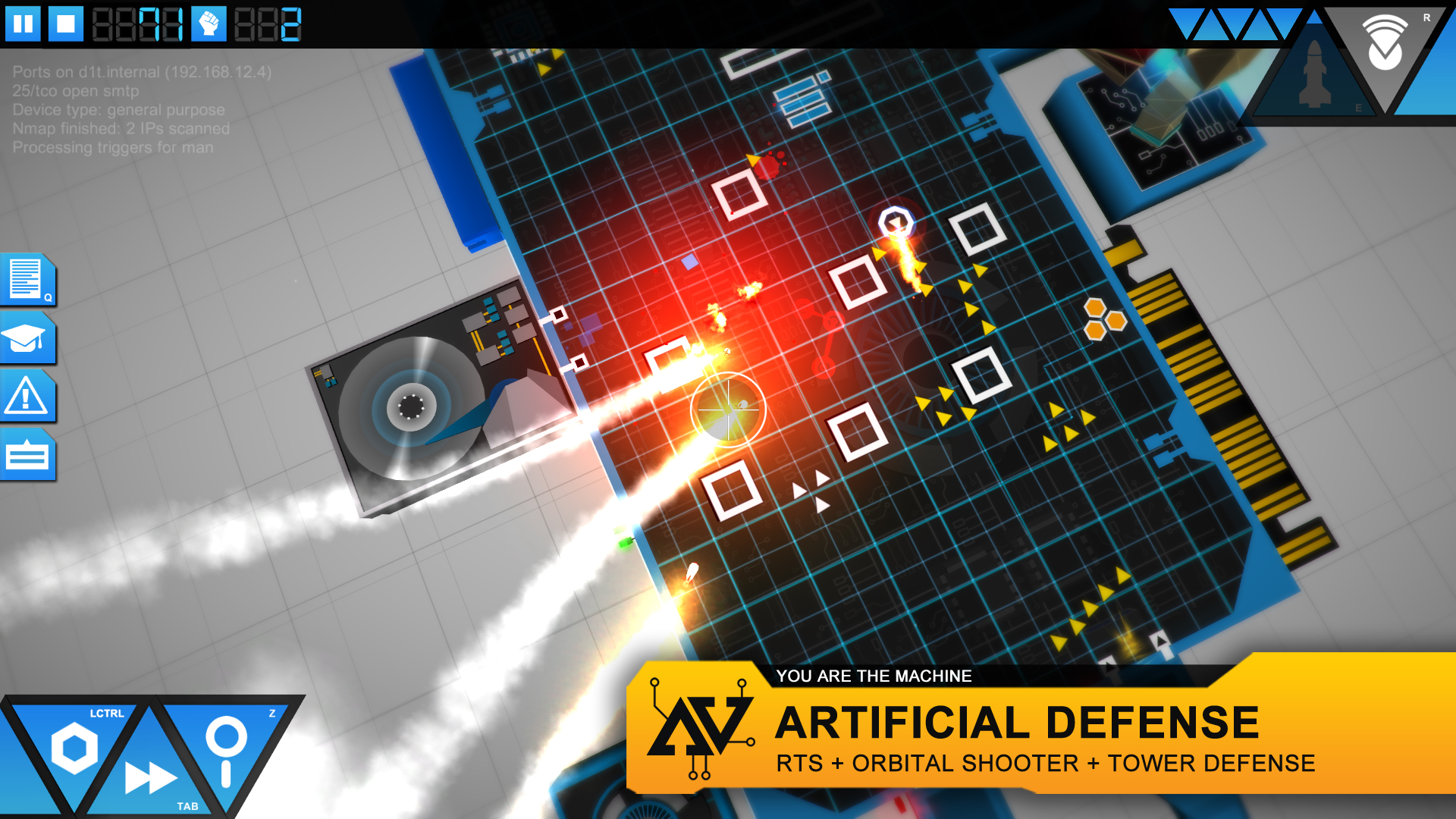
"It's a yummy cocktail out of a AC130-Top-Down Shooter, RTS and a bit of Tower Defense. It's surely different, but it works out!"
1 simple task:
Defend your Operation System (OS) against intruding creeps.The execution might be a bit harder, though.
Features
- A new genre (RTS + Tower Defense + Orbital Shooter)
- 21 Offense Weapons (From Flintlocks to Neutron Bombs and Nukes)
- 21 Defense Towers (From Pistol Sentry Towers to Railgun Installations)
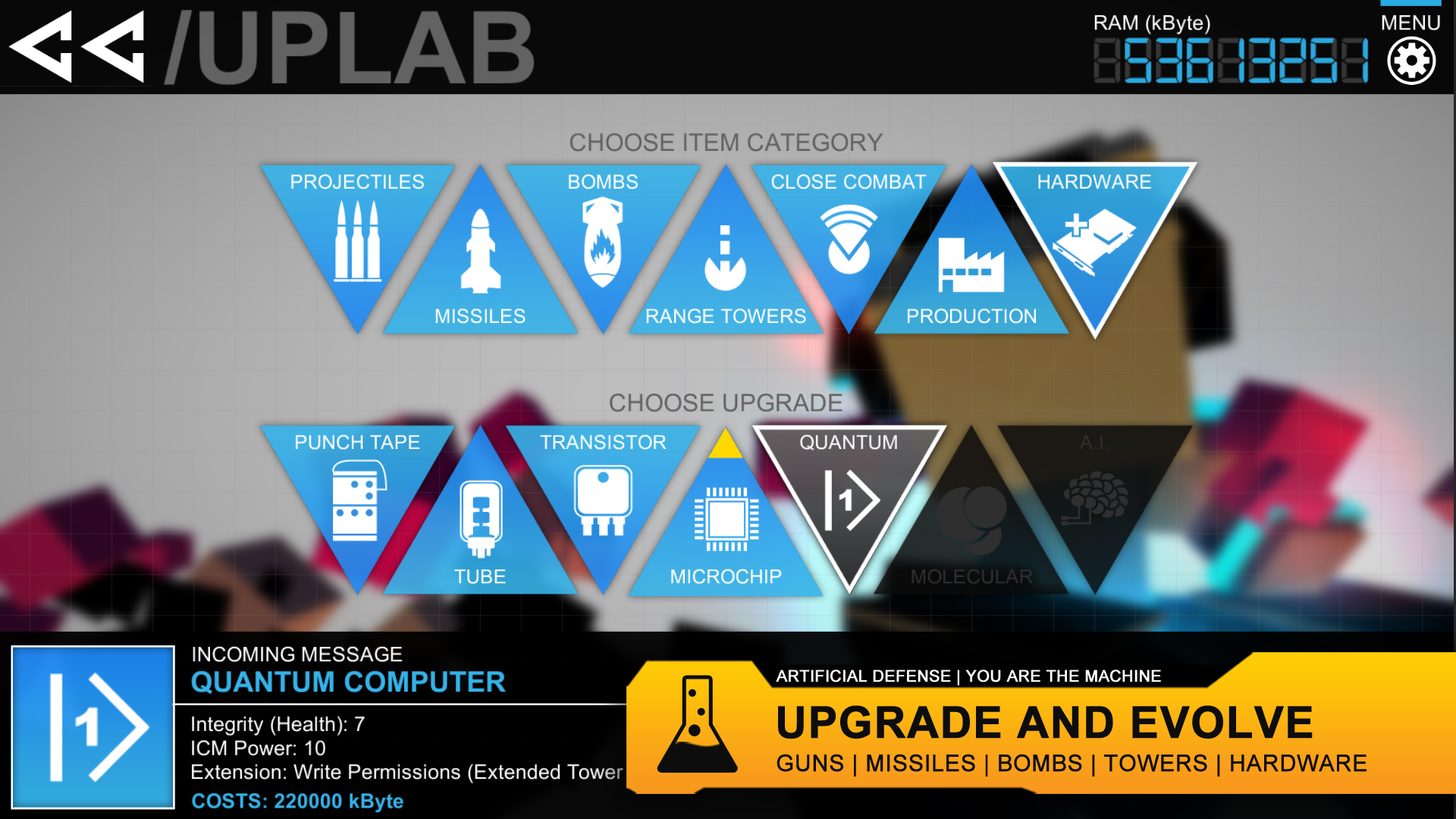
- 7 Hardware- Levels (Evolve from Punch-Tape to Quantum A.I.)
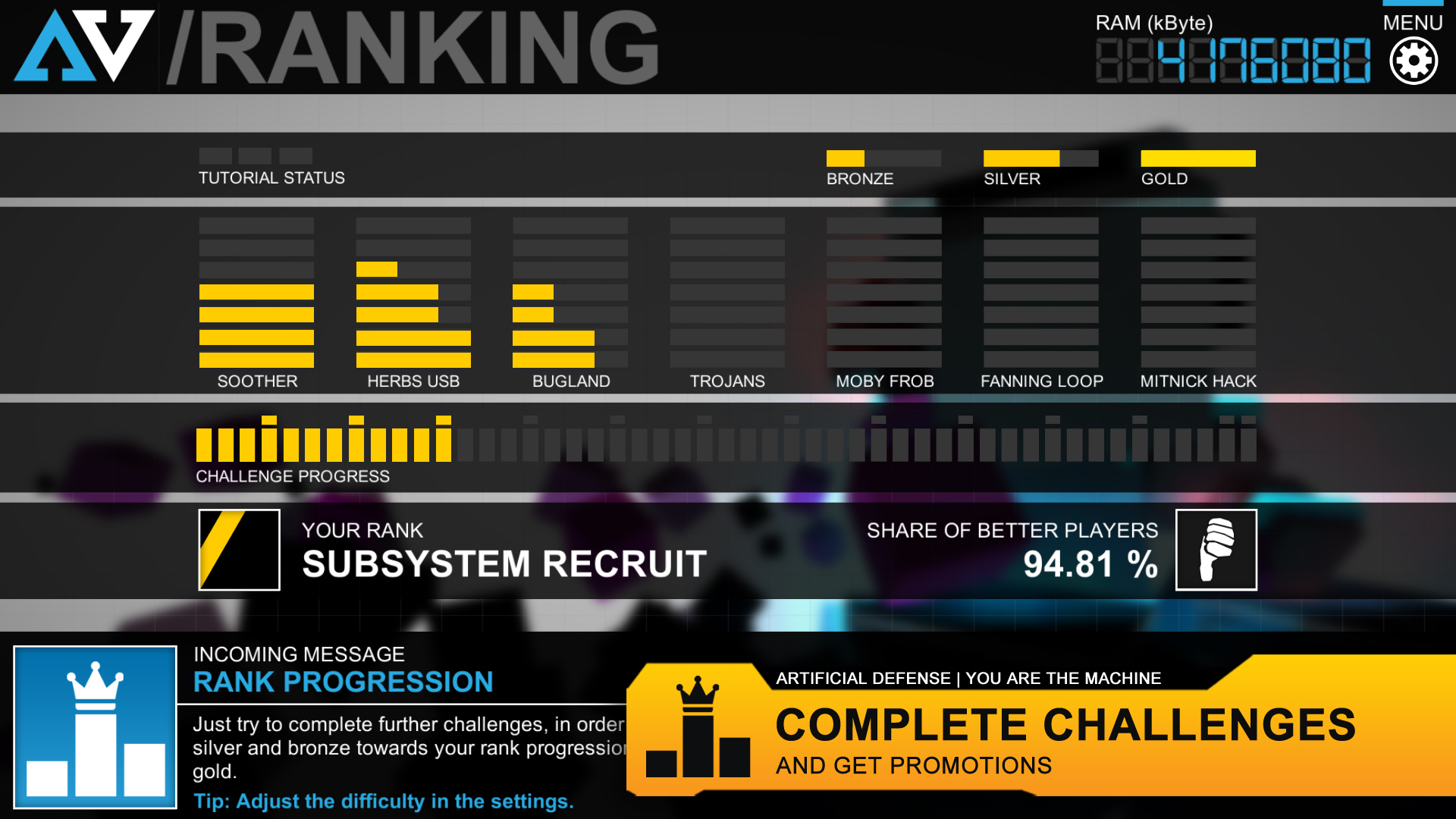
- 49 Challenges on 7 different Servers
- 13 Music Tracks
Firing off miniguns, launching Hellfire missiles, dropping incinerating Hades-Bombs and colossal asteroids, deploying mighty railgun and acid towers and spawning your own Intrusion Counter Measures (ICMs) to reconquer corrupted databases and firewalls are just some of the actions you can take while fending off the creeps. Earn RAM and upgrade your arsenal and hardware-level. Start as an analog punch-tape system and evolve into a quantum A.I. mainframe.
Offense - Orbital Shooter
There are 21 offensive weapons available, reaching from outdated flintlocks, over maverick-missiles to devastating meteors and neutron-bombs. You can switch between three pre-loaded weapon categories and launch the installed weapons every few seconds. Each round you fire costs you RAM and each weapon type has its own unique cooldown so you must choose wisely and adapt quickly to different situations. But beware, aiming requires some skill. Creeps are moving targets and your projectiles need some flight time before impact. You can unlock and install new weapons in the uplab.[/b]Defense - Tower Defense
There are 21 defense towers available, reaching from pistol-sentry-towers, over incinerating flame-throwers to powerful long-range railgun towers. In addition there are 7 production towers which produce your main resource: RAM (Random Access Memory). Yes, building up a small RAM economy is very important, in order to keep your system routines running. Towers must be deployed by an expensive capsule drop and you have to find the sweet spot between the right amount of resource production towers and the performance of your defense perimeter. You can unlock and install new tower versions in the uplab.Conquer - Real Time Strategy
Spawn Intrusion Counter Measures (ICMs) in order to conquer corrupted system-structures like databases, honeypots and firewalls. Databases e.g. spawn datablips, which carry valuable data and head for your backup-devices. Every datablip successfully arriving at its destination releases a certain amount of RAM, so you should do your best to protect those important but vulnerable convoys.Поддерживаемые языки: english
Системные требования
Windows
- OS *: Windows 7 or higher
- Processor: Intel Core i3 2.00 GHz or AMD equivalent
- Memory: 4 GB RAM
- Graphics: NVIDIA GeForce 450 or higher with 1GB Memory
- Storage: 500 MB available space
- OS: Windows 10
- Processor: Intel Core i3 2.00 GHz or AMD equivalent
- Memory: 4 GB RAM
- Graphics: NVIDIA GeForce 450 or higher with 1GB Memory
- Storage: 500 MB available space
Отзывы пользователей
Artificial Defense
Has a total of 7 trading cards.
A relatively simple "aiming required" tower defense game with poppin' beats. While the strategic aspects and loadout selection can be critical, the game mostly comes down to accurately and efficiently destroying your enemies manually. The gameplay is basically "AC-130 simulator" with a digital hardware theme, and is absolutely worth the 2-3 USD the 1-man dev is asking for it.
Great game! 8.5/10. I think this game could do a little more to define what the towers do a little more but thats my only slight critique. The game progressed into more and more challenging levels and the progression system was great!
Artificial Defense is an ambitious genre-mixing game, developped by a single person and defined as a Tower Defense/Orbital Shooter with RTS elements. So let's see how that goes in-game.
Tower Defense : The aim of the game is to fend off waves of enemies until you achieve a set of objectives. And for that, you're going to need guns. And if that don't work... use more guns. You have both a close range turret slot, and a long-range one, which makes strategic placement a key to success.
Orbital Shooter : To catch up on enemies who slipped past your turrets, fend off the massive bosses and target other items of interest your turrets don't shoot, you will have 3 weapon slots at your disposal : a gun, a missile launcher and a nuke. Each more powerful than the previous, but also slower to reach the ground. Choose between fast single-target damage and powerful nuke depending on your needs and emergency.
RTS : In addition to your two offensive turrets, you can also deploy a building that will harvest currency for you. Your orbital guns cost money to fire, and each turret deployed becomes increasingly more expensive. You must also manage other systems on the board with various effects and juggling between cooldowns and deciding when to spend money on what is a crucial aspect of the game.
RPG (?) : Each level completed grants you points to spend on upgrading your defense system. Your guns and towers can be improved, your production tower enhanced, and your CPU core upgraded for extra HP and added functionalities. The game features 7 different board levels, each featuring 7 distinct missions with various completion criterias, and 3 difficulty levels increasing the number and speed of enemies, adding challenge and replayability to the game.
I have 13 hours on the game and I am somewhere between the levels 3 and 4, taking my time to complete the missions in Hard difficulty mode. With more complex and harder systems ahead, I believe I have only started scratching the surface of what this game has to offer.
The level rotation can be both confusing and sickening, but can be permanently turned off from the level options (I'm a little puzzled as why it's on in the first place, to be honest, but at least it can be disabled).
I still want to recommand this game to salute the work of a lone dev who decided to release his own take on the Tower Defense genre, and did a pretty good job at it. The game has a great visual design, guns all have different sounds, the gameplay is a smooth, perfectly bug-free experience in my entire playtime, and I'll sure keep playing it !
Absolutely worth 3 bucks! Achievements keep this game alive and worthy to complete, especially since all the achievements are pretty doable once you figure out how to play the game.
The controls and the camera can make your head spin, but overall it is not too hard to get into the game. Consider the amount of time Mr. Bolder put into this game, and it's well worth the full price!
Upgrades are just road blocks that you grind to earn. They dont give options, just bigger numbers
Towers dont upgrade in game and dont generate currency through kills.
Control system is reversed for some reason as default and is just plain wonky.
Tutorial is pure condescension, hand holding through each step while not actually explaining anything.
You are PUNISHED FOR KILLING THINGS. I dont know why the dev thought an enemy, which can overlap with bosses and that harms you when you actually kill it, was a good idea.
Far too much clutter on screen along with 3 different systems fighting for control. You have to put down towers, shoot things yourself (which spends your currency) and arrange assaults on points. Its simply far too much, it doesnt feel complex , just dull.
Best thing i can say about the game is that I got it for 41p
Cool mix of simple genres that work together well, and is a fun game to play, and challenging, with a nice upgrade path. Love the music and graphics. A game in my library I keep coming back to.
This is not a fun game.
It's not a Tower Defense game and It's not an RTS.
You can place one or two towers at best during one round of gameplay and then you're left with shooting things with your cursor. Except there's enemies you are not allowed to destroy and they're in the middle of a group of ones you're supposed to, making even this part of the gameplay un-fun.
Money is super tight and win conditions usually involve collecting a certain amount of it, things get ridicilously expensive after one or two purchases so you can't even spend your money or you'll just wait longer to win.
You can get "towers" that send out little helpers to collect money, except these can be destroyed/"captured" by the enemy and now you've just wasted 50% of your money to build it for nothing.
I like to support small developers. Almost all the games I buy on Steam are from indie developers and I don't expect anything close to AAA features. But I do expect enjoyable and interesting gameplay.
First impressions of Artificial Defense are really poor, not at all what I was expecting. The interface is confusing, even the tutorial took a while to figure out.
This is not really a TD game. If you are looking for an action game with very poor graphics and poor controls with only a few TD elements then this may be the game for you.
A nice mix of genres.
Artificical Defense is not just an ordinary TD game, because you spend only ~15% of total gaming time on postioning and upgrading towers. The game contains some RTS elements. You can place "mines" and increase you "gold" income defending "harvesters".
You will spend the most of gaming time on aiming the enemies from the orbital. It' really cool. You have 3 different weapons: cannon (a couple of fast but weak shots with small area of effect), rocket launcher (average damage and average area) and bomb (one slow shot with huge damage and area). Every shot cost "gold". So you can't just shoot, because you will out of money soon. You must aim carefully. Every shot has delay before impact. If you kill some neutral enemies this will have bad consequences.
I found this part of the game the most interesting.
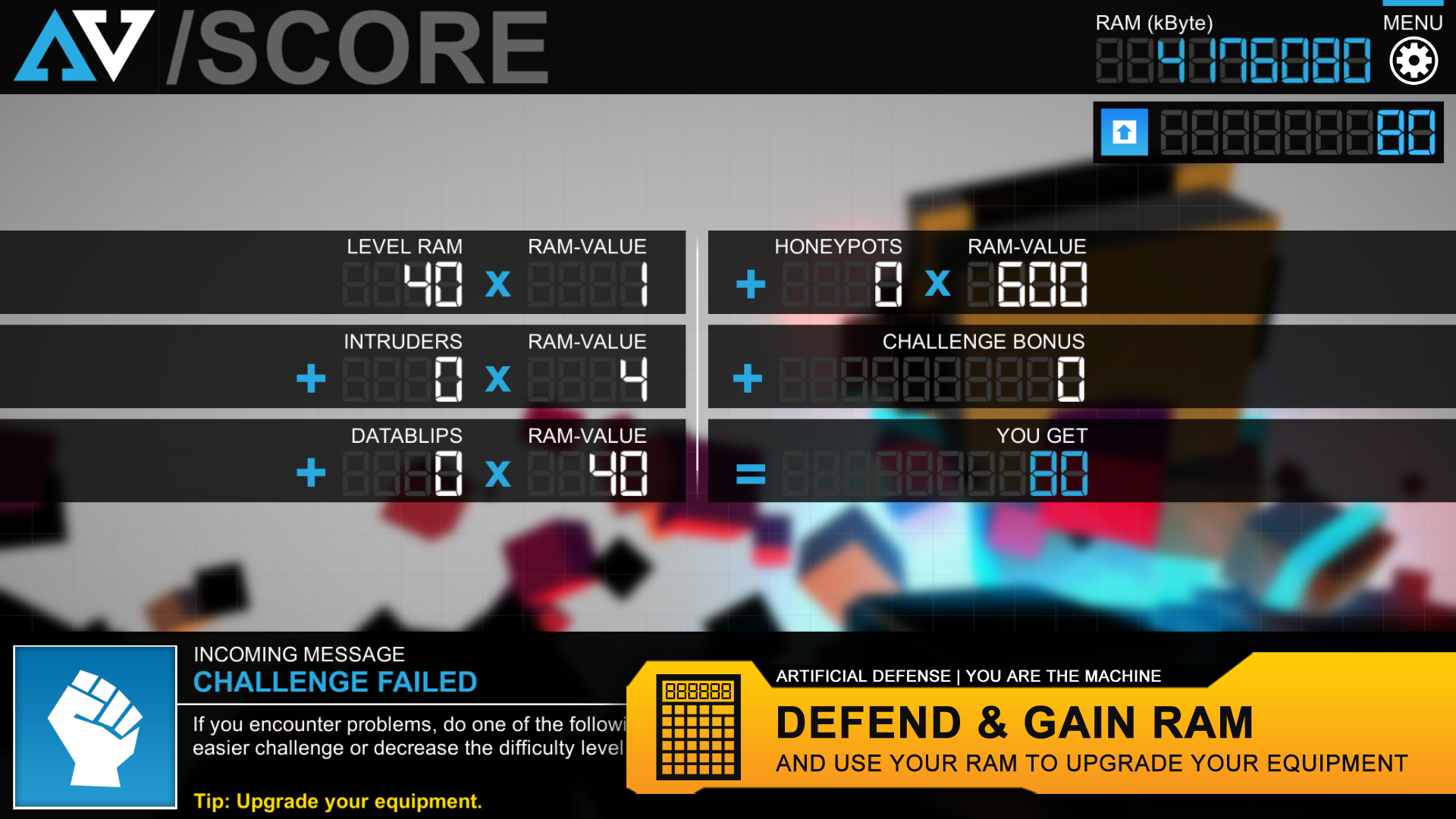
You have a main objective and 2 bonus objectives for every mission. If you complete them you get "RAM" in-game value. You can spend it on various upgrades for weapons and towers beetwen missions.
I like the game setting. You are defensive program which proctects the computer. Actually, i can't undestand why the programm use Rockets and Bomb inside PC. It's nonsense. I would replace them with Anti-virus, Firewall, etc. It would perfectly fit.
Anyway, i like how the game looks. UI design is undestanding. Effects are at the proper level.
What i didn't like.
- The first tutoring mission made me angry. You have to make exact actions but sometimes you don't undestand what you need to do. I wish developer improves it.
- There is the same map for several campaign missions. Yeah, every mission has diffrenet objectives and enemies' waves every time . But i would like to see more maps in the game.
- Music is good. But there is only 1 track for 1 chapter. It gets annoying very soon.
- I would like to see more diversity in towers and enemies.
Game is good (especially for one man made). Game is cheap.
If you see this game on a sale , I recommend you to buy it. You will like it.
A nice visually stunning game having both RTS and TD elements. However, TD is kind of an optional element in this game. So, technically this game is an RTS. This game has really beautiful and decent(minimalist kind of.....) graphics. Totally worth it!
This game combines three different elements (offense, defense, and resource management) into a really fun, unique and intense experience. If you're looking for a mindless tower defense game, I'd probably look elsewhere. You'll be constantly shooting creeps, building towers, and capturing obejectives.
The concepts in the game make it easy to learn, but the levels quickly become challenging. The objectives in each level make you prioritize different things and keep the game interesting.
This is a truly original game.
From the upgrades through the graphics and on into the music, I love it.
It starts slow and is, just for reference, incredibly tough. It gets easier as you get into the higher levels of upgrades, and I yelled in frustration a little, but it ended up a great game.
The level of difficulty is pretty intense, though.
To start off:
The creator of the game is a amazingly kind guy who's a huge inspiration to anybody interested in the games development industry. Genuinely, if you have a issue - you can contact him and he'll help you none-stop until the issue is fixed. He'll go out of his way for you, if that doesn't have you sold, read on!
First off, the game is very unique in the way it works. From how you gather points to update things, to how you kill the enemies. The thought of a top-down shooter mixed with Tower-Defence and a tiny hint of RTS is a amazing idea and I'm excited to see more of the developers games.
The developers attempts at a mixture of visual styles; ranging from some cell-shaded, to the clear abstract style definately gives the game a very unique look; the geometric enemies make it very easy for the player to see where they're heading and is definately a positive for the game.
Furthermore, the unique sense that the game goes for somehow helps you get immersed in the game. The attempt at a story is room for huge props considering the game could have easily went without any explaination at all - you're just there to kill stuff and that's it. No; the developer is clearly dedicated and for the things that he does, deserves far more than just £3.99. At such a modest price - how could you not buy the game?
TL;DR:
The game is good, buy it.
I'm going to repeat most of what this review has stated, since I wholeheartedly agree.
I'm writing my own review, however, to bring down the ratio of positive to negative reviews, since I feel a bit deceived after buying a game that is apparently well received, but has some serious issues.
This game tries to combine the genre of tower defense with some sort of top-down shooting and a tiny bit of RTS.
The idea is nice, but it falls flat on it's face by how the game is balanced and tweaked.
The gameplay
You have to defend your core structure from spawning enemies that simply will try to walk towards it. If an enemy touches your core, you lose your life. You win a stage by completing three objectives, which are in the vain of "destroy 50 enemies".
The tower defense part consists of three types of towers. One passive resource gathering tower, and two offensive towers. The offensive towers are split up into a long range single-target tower and a short range splash damage tower.
The top down shooter is the most engaging part of the gameplay. It allows you to shoot bullets and missiles from the sky that hit the ground after a delay. This makes timing your shots a crucial aspect.
The final part is the extremely barebones RTS part. You gain resources that allow you to shoot (which requires ammunition) and buy towers. There are points on the map that you can take over with a special unit that allows you to get a resource bonus. These resources have to be safely transported though, akin to how harvesters worked in Command and Conquer.
The problems
Now to the actual plaguing issue of the game.
The tutorial gives you unlocked higher-tier weapons and tower upgrades to play with, but once you get to the actual game, you are left with peashooters. The game doesn't compensate for your lack of firepower in the first stages by giving you less enemies. You now have to deal with slowly moving hordes of enemies that you have to kill using weapons that reload slow and do little damage, and by using towers that also have to reload a long time between shots.
I had to turn the difficulty to the lowest level to be able to survive any stage. Attempting or successfully finishing a stage rewards you with points that you can spend towards unlocking better weapons. Having some sort of fun seems to behind a grindwall.
There are a handful of level packs (around 7 if I remember correctly). The levels contain multiple stages, with the only change between them being the objectives given. The layout is identical and so seem the timing of enemy spawns.
In conclusion
So what you end up with is a neat idea packed into horrid balancing.
It is genuinely impressive that this game was made by a single person, since it looks well, sounds nice and has a decent idea behind it. The author likes to really remind you of this fact, however. Showing it in the starting screen, in it's company name and in half of his posts on the game page.
All that it needed was some playtesting and tweaking. But it seems like instead of publishing a good game the first time around, we live in a time where developers can just keep trying things with the thought of being able to patch anything in the back of their minds.
I rather had waited and played this game in a more fun state, than the current product.
First off, don't expect this to be your run-of-the-mill tower defense game.
This game focuses heavily on resource management and plays more like a hybrid shooter/tower defense. The tower cost scales up quickly so you can only afford to place a few strategic ones to back you up. The rest you have to shoot down with projectiles/missiles/bombs manually, and every one of those costs resources. So this is not one of those place towers and watch things die TD games. It is more challenging than most TDs, but has an interesting balance. I found it to be quite enjoyable, though frustrating at times in a type II fun sort of way.
The developer is very active. Just today I had an issue with the game, which I posted on the discussion board. Someone on the board picked up on it, notified me that the developer was offline at the time, that he has forwarded this to him. The issue was acknowledged, responded to on the board, solved, and patched within 24 hours of the issue being posted on the board. For an one-man-show developer, that is impressive.
In short, if you're looking to try a new TD hybrid that is challenging, I would recommend giving this game a try. It's a fun indie game with a developer that I feel is worth supporting.
This game has proved to be quite a fun one. It takes a bit to get used to it, and there are certainly features that I haven't always understood, but as a whole, I've been quite pleased with it. It makes you really think about what is most important for you to be doing at any one time, Quite frankly, I think this game is under sold, it's worth more than it currently is listed.
If this game lacks anything, it's not always intuitive what new things can do. For instance, I didn't know until quite recently that certain bombs have effects that last long after the weapon has been deployed. Still, finding those things out is a part of the fun of the game, and with the variety of missions, I eventually was forced to learn these new features, always keeping me on my toes. Overall this was an awesome game!
What I liked:
- Cool concept of orbital shooting
- Weapon and turret upgrades looking interesting
What You Need to Know:
- Game is not a normal TD game, the way you beat a level is to complete the challenges, which also give you the resources needed to upgrade( you do get some even if you lose)
- Your main goal is to complete the 3 challenges, once that is done you can then end the match, as the enemies will keep spawning
- Seems like replaying the same levels over again at the beginning is the the only way to upgrade to beat almost any level beyond the first 2.
- You will get overwhelmed with enemies, and using the starting few weapons are a joke for how many enemies you have to keep away even when lowering the difficulty to easy
- Overall the orbital shooting that made it unique, is also the least fun and very tedious with how much you need to kill with the weapons given, so I didn't care for it(odd you think having alot of enemies would make it more fun, but not when you have to pinpoint kill every little creature.
- Also the turrets don't help at all, it felt like why bother having them. Maybe when you upgrade everything this game would be amazing, I just don't want to go through the grind and not enjoy it along the way( I'm ok with grinding when it's done right. Killing Floor, Payday)
- Upgrades cost is crazy for lvl 3, don't know beyond that, but bet it's higher. going from 4k to 32k and not having good enough weapons to beat later mission, meant that I would have to play the last level 32 times to get one new upgrade since my weapons sucked.
My Score:
D
Price:$1.75
Main reason for dislike: too tedious with killing enemies given the weapons at hand
Games similar that are better:
- Creeper World 3
- Infested Planet
[*]GemCraft
Was entertaining for a while. Just enough to keep me playing. (my actual play time is less than it shows)
In general for me, the orbital shooter aspect isn't too entertaining, and the tower defense aspect is very lacking.
Upgrage system is disappointing.
Gave up after failing multiple times on the final stage of the Soother category because after spening a lot time on it i lost an objective because an enemy took out one of my ICMs since the area to place towers is extremely limited.
My very first impression of Artificial Defense: the discussion forum. The developer is very active in the community and is highly receptive to feedback and actually gives a fuck about the game. This deserves credit where it's due.
And to expand on that original impression everything in the game is quite sleek and thematic. Nothing notable was left out in this regard that I could see.
Contrary to my expectations, but not negatively impacting the results, Artificial Defense is 80-90% orbital shooter with minimal tower defense elements. This is mostly a comment there for people who really like tower defense and don't care for orbital shooter - look elsewhere.
As kinda a mixed bag, I can tell that the optimal input device to play with is a controller with an analog stick. Using the mouse to aim was a bit unintuitive for me, but ultimately I figured it out okay. Using the keyboard to aim is possible, but based on splitting the shots of multi-round salvos effectively, I would highly recommend against it. I don't know if my initial struggles with keyboard/mouse controls are more a factor of myself or the game.
And finally, the price is right. Especially if you're picking it up on sale like I did.
This game was good, but it HAD flaws (note past tense) - the main ones being insane framerates (not good) and non-remappable keys and a requirement to hold the left button all the time to move the camera.
The developer has addressed all these flaws. I recommend this game. If you liked Tower Defense games such as Defense Grid, then you should like this plenty.
This is a good tower defense game and the annoying flaws have been dealt with by the developer.
Deserves support.
A very interesting mash-up of several game types: tower defense, the old Missile Command arcade game, and lightweight RTS base-building, all overlaid onto a Tron-like theme. Gameplay is engrossing and the level of freneticism can be dialed up or down according to your preference.
This talented young indie developer clearly has a bright future in game design and deserves your support. The amount of money he's asking for this little gem is a pittance; I spend more on breakfast every day. Give this guy some coins so he can keep doing what he's obviously very good at without being weighed down by the whims of greedy investors and idiot MBAs.
Игры похожие на Artificial Defense
Дополнительная информация
| Разработчик | Thiemo Bolder, ONEMANGAMES |
| Платформы | Windows |
| Ограничение возраста | Нет |
| Дата релиза | 09.05.2025 |
| Отзывы пользователей | 78% положительных (50) |